How To Conduct A Threat Analysis Trying to find a method to stay arranged? Free printable schedules are the best service! Whether you need a daily, weekly, or monthly planner, these templates assist you improve jobs, manage your time, and boost efficiency. Created for versatility, they're perfect for work, school, or home use. Merely download, print, and begin preparing your days with ease.
With personalized options, free printable schedules let you tailor your plans to fit your distinct requirements. From colorful styles to minimalist designs, there's something for everybody. They're not only useful however likewise a budget-friendly method to monitor consultations, deadlines, and goals. Get started today and experience the distinction a well-organized schedule can make!
How To Conduct A Threat Analysis

How To Conduct A Threat Analysis
Download your free password log printable Being organized but having the flexibility to do it my way is what a password log template is my jam Password Logs – 25 Free Password Templates ... Organizing passwords and other sensitive information has never been easier. Use these password logs to keep the ...
7 Free Printable Password Keeper Printables to Download Instantly
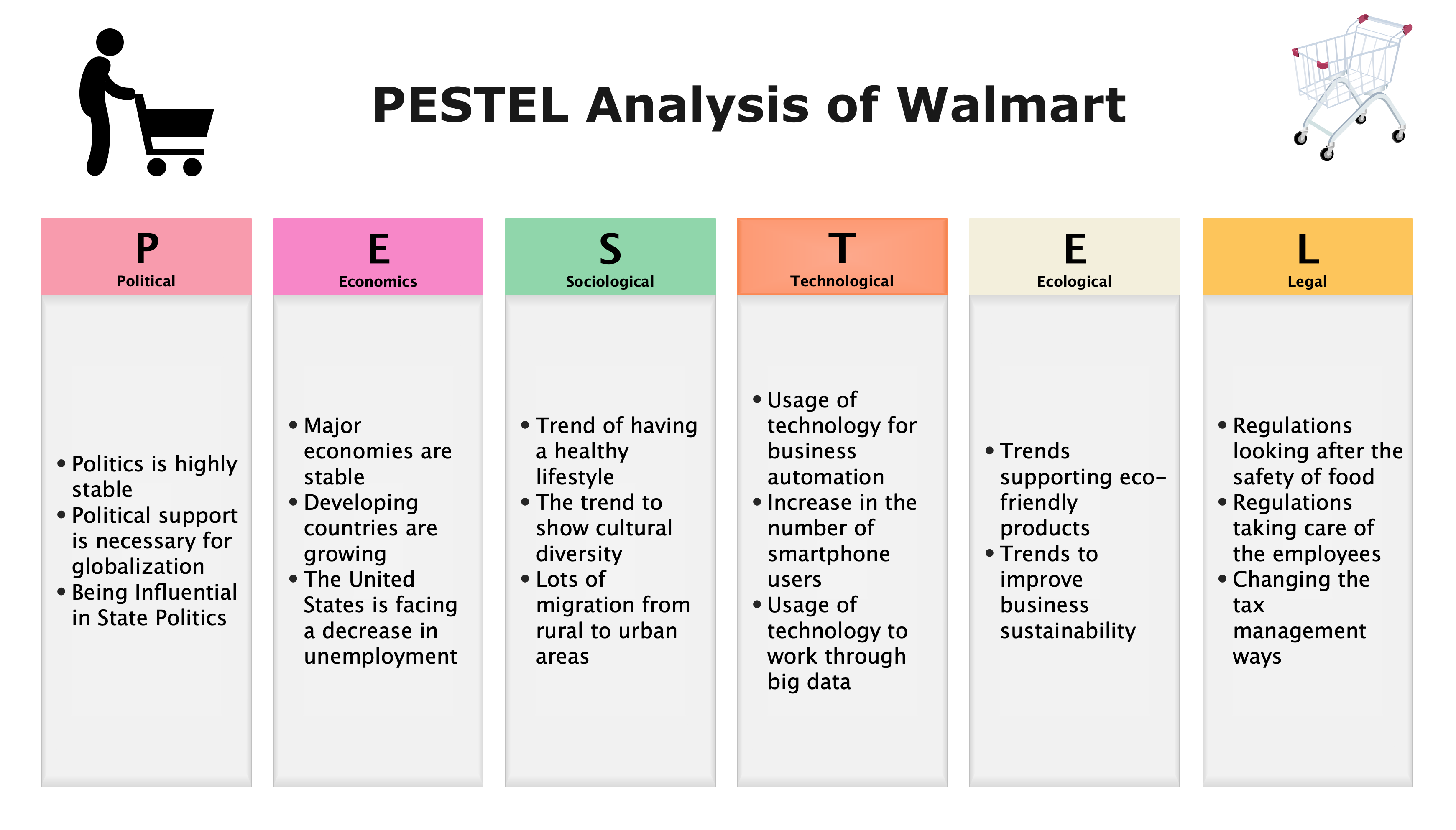
Pestel Analysis
How To Conduct A Threat Analysis8 Cute printable password log templates you can use to keep your passwords safe and organized! Cute & easy-print password trackers. These password logs come in 25 different styles and they re free to print and use for personal use only Use these password logs in your
Looking for a pretty password tracker printable? Super! Here you can find 14 different printable password trackers, perfect for organizing all your login info. Feasibility Study Resources Global Professionals Salary
Password Templates World of Printables
PUKAW TANLAG PUKAW TANLAG WITH BEN SUMOG OY 03 00PM 06 00PM
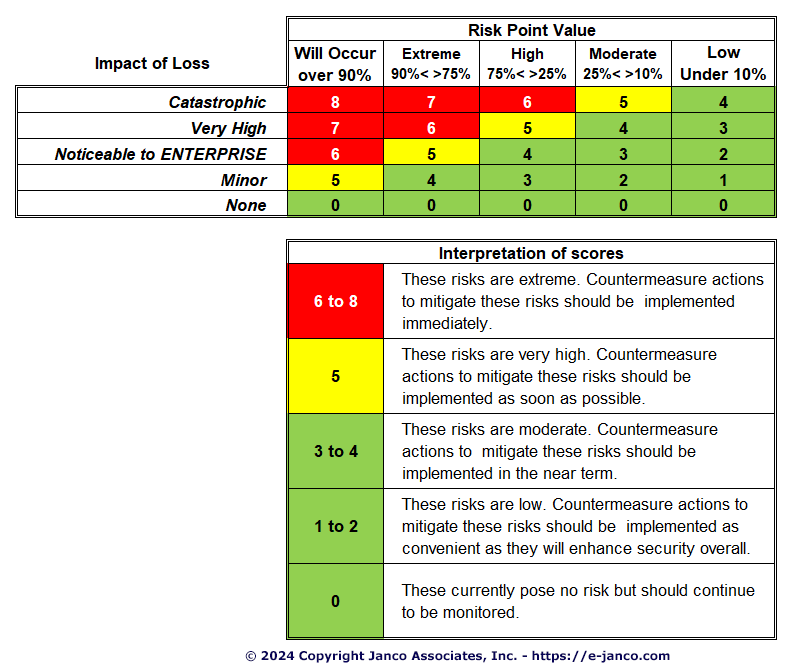
Password log templates choose from 20 designs and layouts to download and print to organize your passwords and usernames on one page Threat Vulnerability Assessment Tool
PRINTABLE PASSWORD KEEPER WEBSITE WEBSITE USERNAME USERNAME PASSWORD PASSWORD EMAIL EMAIL SECURITY ANSWERS SECURITY ANSWERS DATE LAST CHANGED How To Properly Conduct A Breast Exam At Home Breakfast Television Threat Assessment Certification Prntbl concejomunicipaldechinu gov co
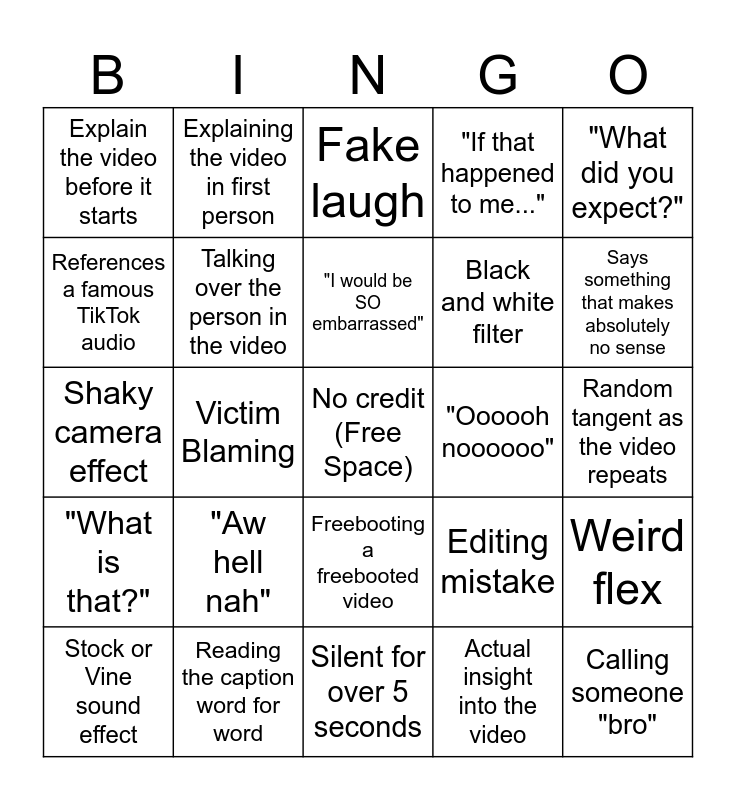
Sssniperwolf Bingo Card
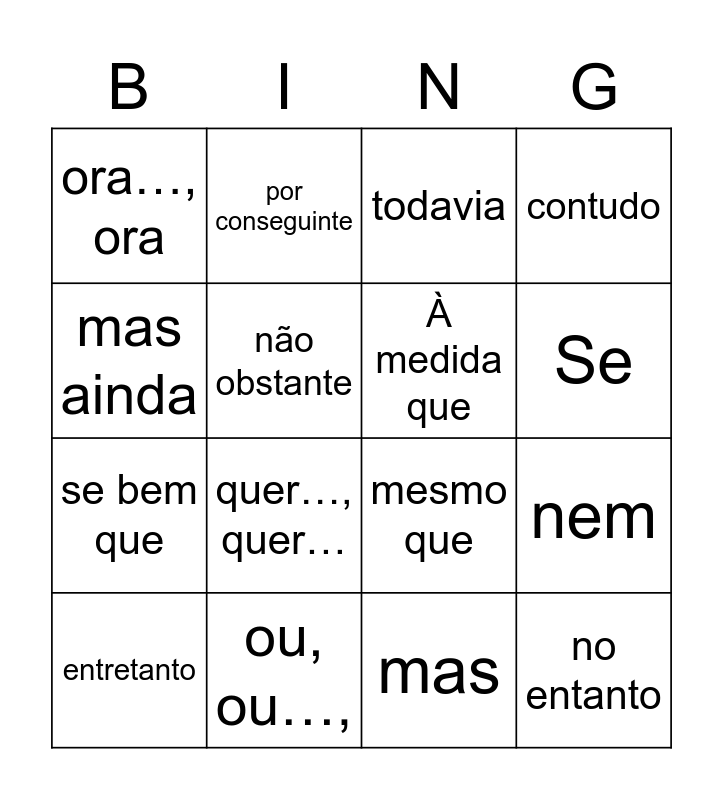
Bingo Das Conjun es Bingo Card

CORE Financial Inc Measure Your Risk

Our Replication Process

Marketing
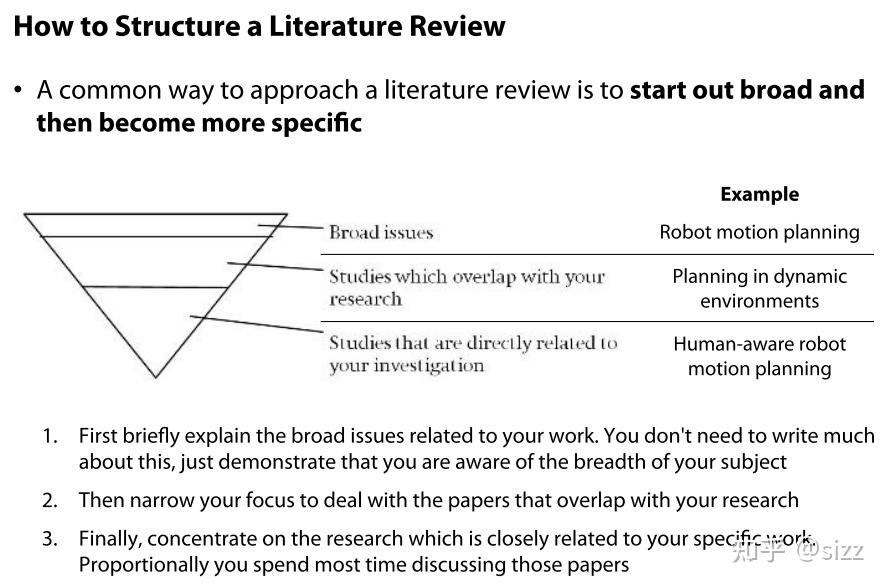
How To Conduct A Literature Survey
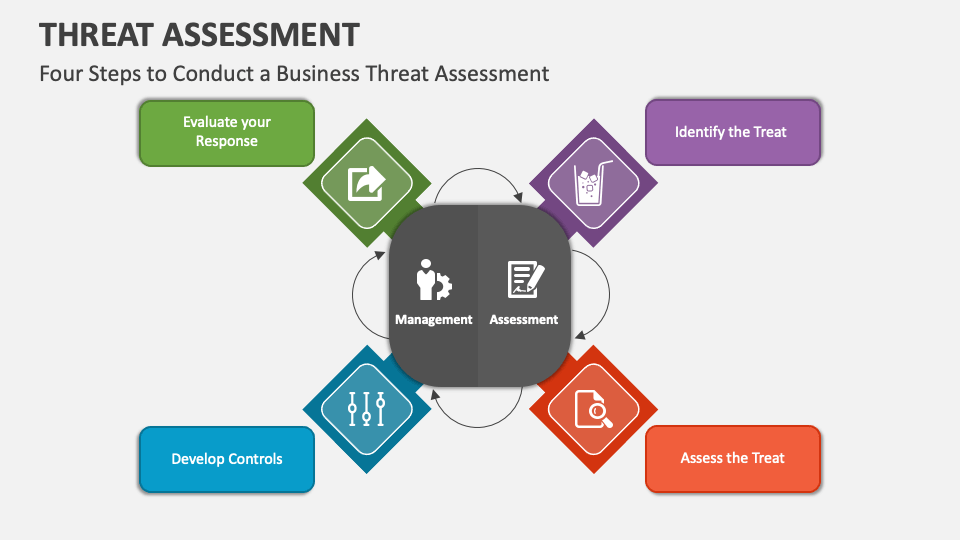
Threat Assessment PowerPoint Presentation Slides PPT Template
Threat Vulnerability Assessment Tool
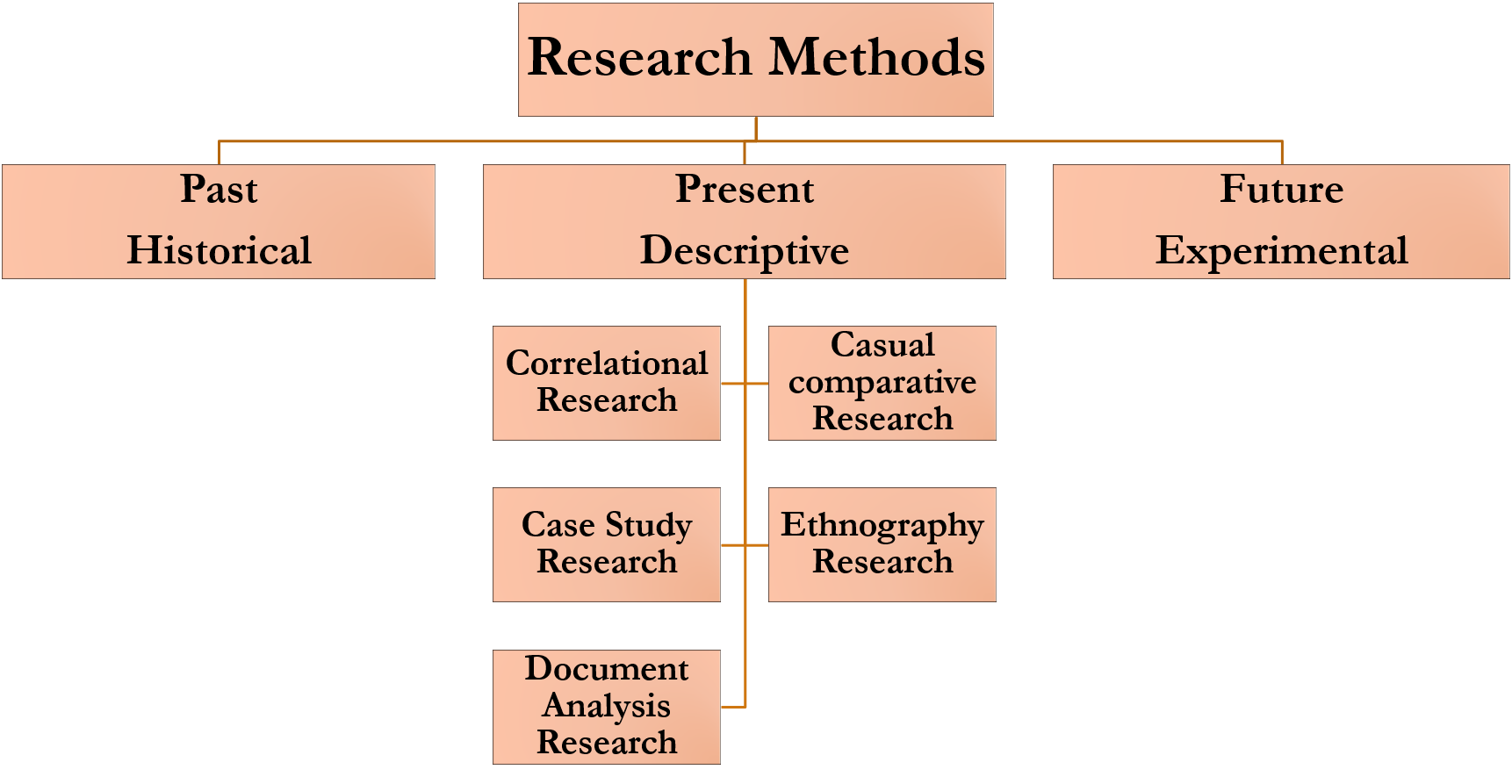
Descriptive Research Design
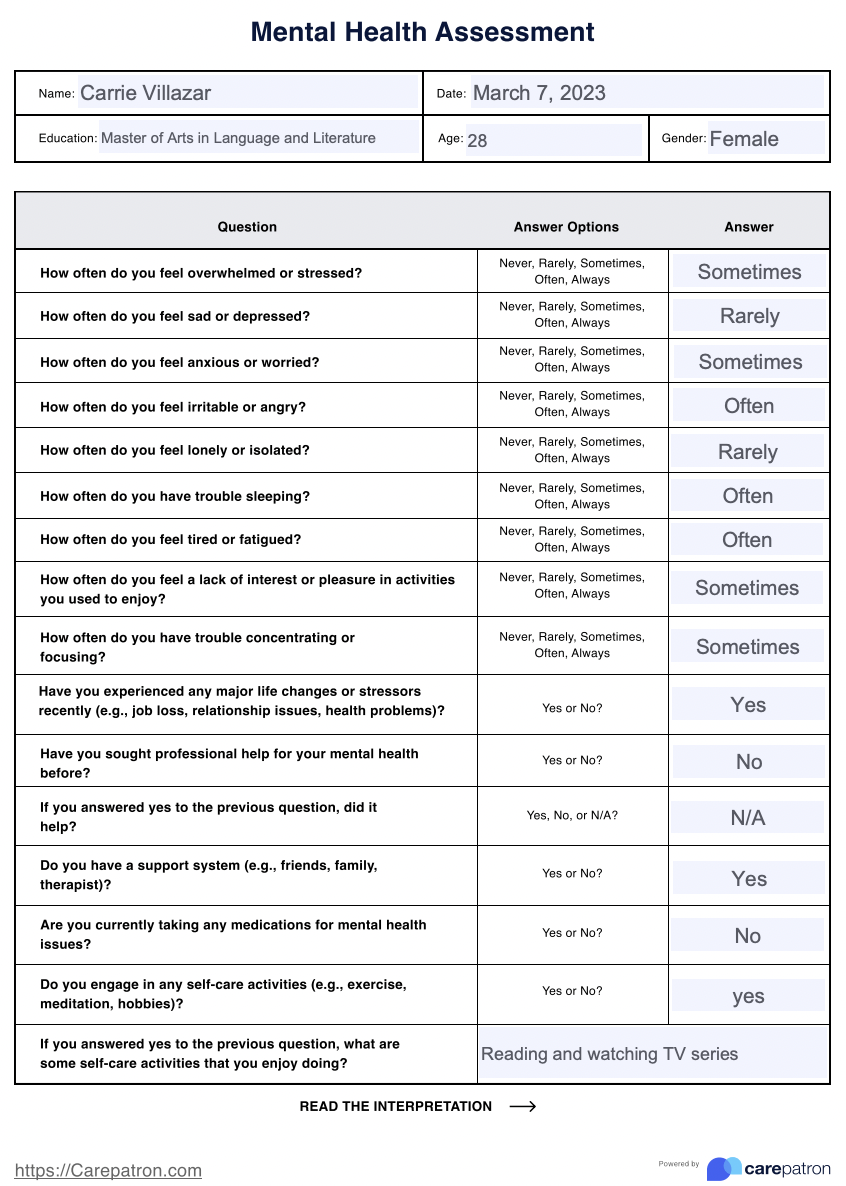
Emotional Health Examples